This is an internal documentation. There is a good chance you’re looking for something else. See Disclaimer.
Pseudo-VPN using SOCKS5 over SSH
This page documents how SSH can be used as a pseudo-VPN. First, a SSH tunnel needs to be opened with a local SOCKS5 endpoint. Once that’s done, any application supporting SOCKS5 (e.g. Firefox) can be configured to tunnel traffic through the tunnel.
To connect to the office network use either backup02.tocco.ch or git.tocco.ch as server name in the following steps.
Hint
For admins:
In order to grant tunnel access only, grant @remote access to the user as described in SSH Server Access / Emergency Access (Ansible).
Setup SOCKS5 Tunnel on Linux
If you haven’t setup up ssh yet, set it up according to Set up SSH.
Open tunnel:
$ ssh -D 3333 -N tocco-proxy@git.tocco.ch
Setup SOCKS5 Tunnel on Windows
Open Putty Key Generator and generate a key:
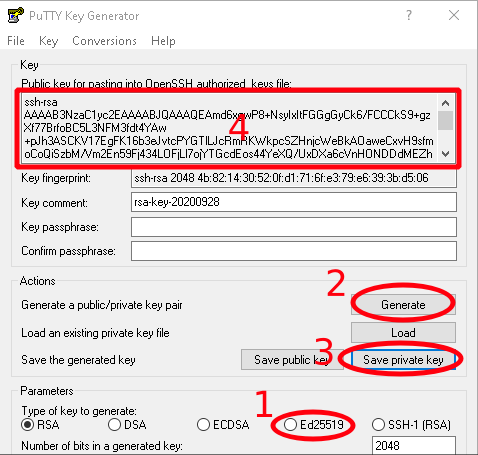
Putty Key Generator
Select type Ed25519.
Generate a key.
Save your private key. Remember the location.
Copy the public key and forward it to operations to allow them to grant to you access.
Open Putty and configure it as follows:
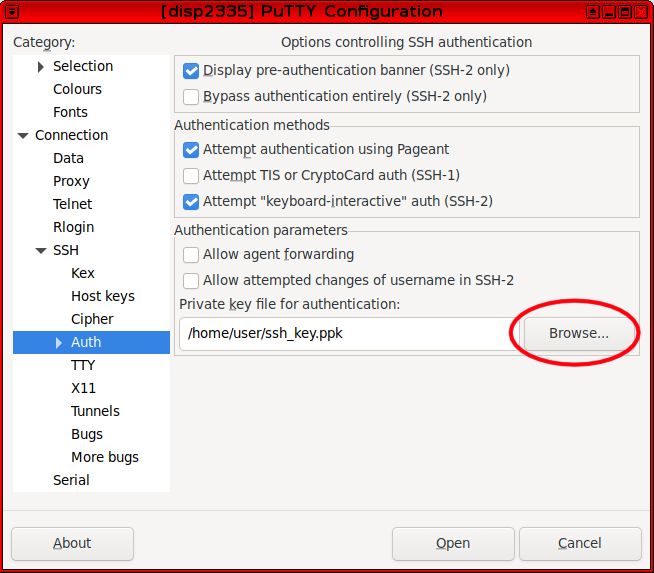
Connection → SSH → Auth
Use the key you stored in the previous step.
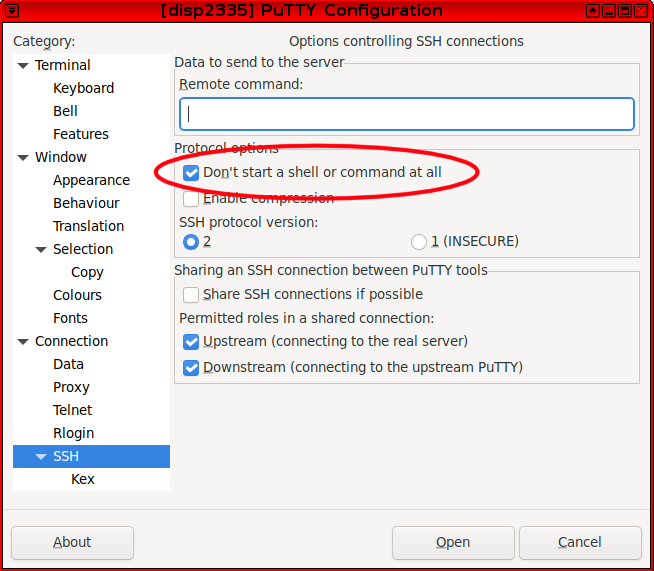
Connection → SSH
Check Don’t start a shell or command at all.
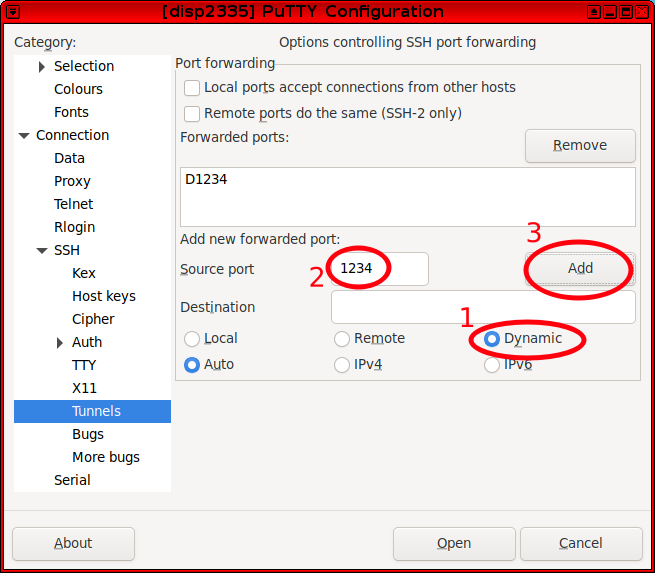
Connection → SSH → Tunnels
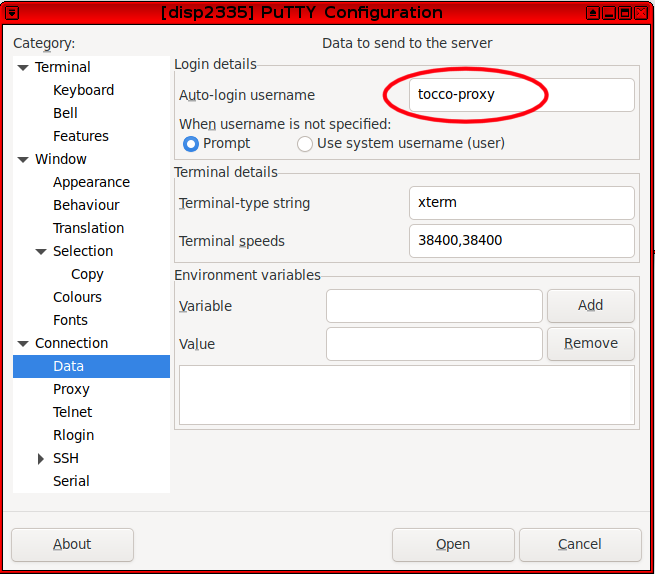
Connection → Data
Use tocco-proxy as username.
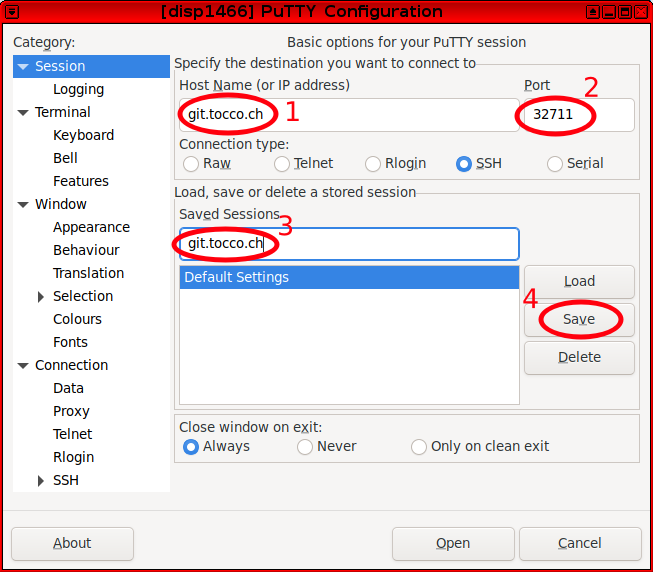
Session
Set host name git.tocco.ch (or alternively backup02.tocco.ch).
Set port 32711.
Set a name for the session.
Save the session.
Open tunnel:
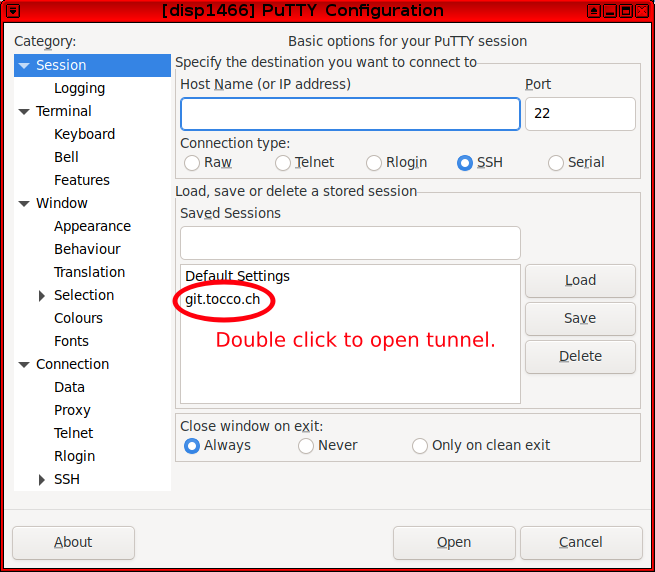
Session
Once the session has been saved, double click on the name to connect and open a pseudo-VPN tunnel.
To connect in the future, open Putty again and repeat this step.
Use SOCKS5 Tunnel in Firefox
Once the tunnel is open, you can configure a SOCKS5 proxy in Firefox to use it as pseudo-VPN.
Open Settings in Firefox
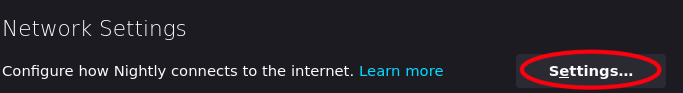
Search and open Network Settings
Set a proxy
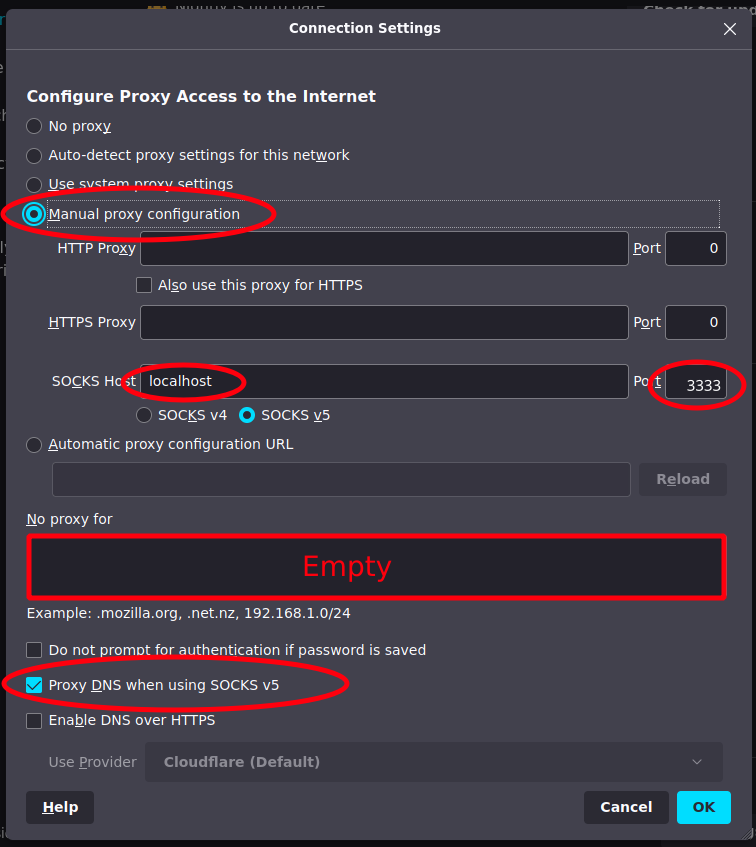
Make sure to disable proxy settings again